|
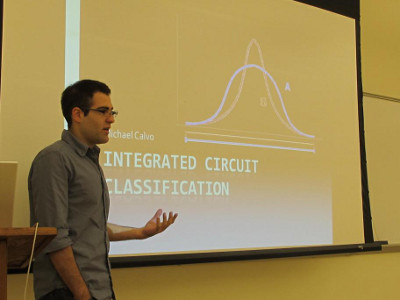
Michael Calvo, Eastern Connecticut State University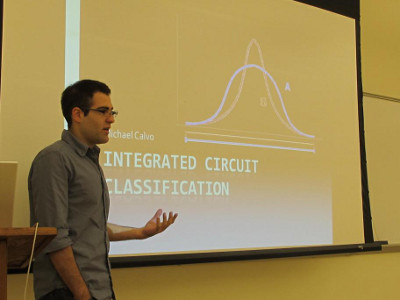
Integrated Circuit Classification
|
|
Andrew Ferraiulo, University of Connecticut
Globalization has allowed Integrated Circuit designers to outsource their fabrication needs. Though this has reduced IC production costs substantially it has introduced a new security and trust concern: an adversary at an untrusted fabrication facility could introduced malicious circuitry into the IC. These malicious circuits, called Hardware Trojans, could disable functionality, reduce performance, or surrender control of the device to the adversary. During Andrew’s work with the REU program, he examined a Hardware Trojan detection method which has been deemed likely to succeed: The On-Chip Ring Oscillator Network(RON). Andrew explored its limitations and examined the affect of various design parameters bringing it closer to being implementable on real practical devices.
|
|
Stephanie Greene, MIT
NetCog: Scoring Subsystem Improvement
As malware becomes more prevalent and clever, the need for a reliable detection system becomes more important. NetCog will fill this need. It uses the network traffic to pinpoint specific network behaviors. It does this by implementing a feature extractor and a scoring subsystem. The scoring subsystem first selects a set of features from those collected by the feature extractor. It then groups them into hyperplanes, with each axis representing one feature. The network flows (traffic between two specific computers) are mapped into the hyperplanes and divided into clusters. Using a rank function which assigns a weight to each cluster, each host is assigned a score defined as the sum of the weights of its clusters plus the product of the weights of its clusters multiplied by a social factor. The social factor is useful in cases where the target behavior is frequently exhibited in groups of hosts, but can be omitted for other targets.Stephanie was responsible for finding a rank function that results in scores that accurately predict whether a host exhibits the target behavior.
First she clustered the targets using k means clustering, quality threshold clustering, or hierarchical clustering. Then she defined the rank of each cluster as either the minimum distance between that cluster and any target cluster or as the sum or product of the distances between that cluster and all target clusters. After testing a number of different parameters (the number of clusters in the case of k means, the maximum diameter for quality threshold clustering, or the threshold value for hierarchical clustering), Stephanie determined that the current approach needs a bit of refining. In future, Stephanie would like to examine data reduction techniques so that the network flows can be clustered in different ways, use a different set of features since another set might have more predictive power, and testing this on a data set that includes more targets so that a few targets exhibiting atypical behavior will have a smaller impact on the results.
|
Philip Hubert, Dickinson College |
|
Mandy Korpusik, Olin College
Simulating Data Deduplication Security for Cloud Storage
An important area of computer security today is cloud storage security because of the current technology trend where many users are storing more data online with the cloud. Cloud storage providers use data deduplication to ensure that each file is stored only once, which could give providers access to clients’ file contents or information about which files clients own and share with other clients. Three levels of increasing security to address this concern are encryption (the contents of the file are encoded so that only the provider has the key to decode the file), convergent encryption (each client has its own key so that the storage provider cannot access the file’s contents), and distributed convergent encryption (the storage provider does not even know which files a client owns because the information is distributed among all the clients). Mandy wrote a client-server network simulation using the simulation framework OMNeT++ in order to investigate how much more time is required with each of these security levels for clients to store data on the cloud.
|
|
Robert Martin, Eastern Connecticut State University
Creating smaller and more advanced computer circuit boards has been a challenge facing the technological aspect of our world. Recently a new discovery was created, called the memristor, and with this new object we can take one large step towards the future of computer technology. This discovery will be able to improve simulating the nervous system due to its similar characteristics to the human brain. Future research is needed to fully understand the memristor and its usage in our everyday life.
|
|
Michael Roberson, University of Connecticut
The National Institute of Standards and Technology (NIST) is holding an open competition to find a replacement hash function algorithm for their Secure Hash Algorithm (SHA) standard. Currently there are five finalists in the competition: Keccak, Blake, Grostl, JH, and Skein. The winner is expected to be announced in 2012 and will be known as SHA-3. Our goal is to optimize implementations of each of these SHA-3 candidates in the C programming language for the Texas Instruments TMS320C6740 DSP so that we may assess the performance of this DSP platform relative to other devices with varying speed, power consumption, and area characteristics. The TMS320C6740 has two nearly identical datapaths, each with four functional units capable of performing operations in parallel. Each of the five finalist teams have reference implementations of their respective algorithms, which Michael analyzed to identify operations that may be performed in parallel and optimal arrangements of these instructions to maximize the parallel usage of the DSP’s eight functional units.Presently, Michael’s optimization of the Keccak team’s 32-bit bit-interleaved implementation hashes a short message with a 64-bit word length and 1,024-bit bitrate in 3,208 cycles or approximately 25 cycles per byte.
According to the Keccak team, the next highest performing 32-bit platform implementation of a short message at the same word length and bitrate is 5,060 cycles or approximately 39.5 cycles per byte on the Intel Pentium M processor. Michael also focused on the Blake algorithm. The modifications of the Blake team’s 32-bit implementation currently only yields results of approximately 33.4 cycles per byte for Blake-512 while performance data for Blake-512 on many other 32-bit platforms is consistently below 15 cycles per byte.
|
|
Owen Search, University of Connecticut
Karl Severin, Eastern Connecticut State University

On the Importance of SCA (Side Channel Analysis) Resilience Evaluation Owen and Karl contributed to a research group studying the threat of a hacking attack known as side channel analysis. Of considerable import to digital computing systems, this type of attack exploits the physical characteristics of a target system (such as power consumption, electromagnetic radiation, etc) in order to retrieve sensitive data. The iteration of this attack currently of great interest to the hardware security community is power analysis, which examines the statistical correlation between target data flowing through a system to the power consumed during such an operation. This attack, originally proposed by Paul Kocher in 1999, has been proven to exploit real vulnerabilities in cryptographic systems that perform supposedly “secure” operations commonly implemented in a vast array of sensitive systems.

As digital technology increasingly affects our everyday lives, both public and private, there is an obvious need for reliably secure computing systems.
The research group that hosted the research is concerned with developing a model for evaluating the resilience of a system to SCA attacks. Owen’s contribution consisted of generating simulated data that will be used to examine the SCA resilience of a cryptographic computer chip implemented on a variety of different technologies. The simulations Owen performed provide data that may shed light on how the resilience of the module is affected by both the functional design and the technology used for implementation. There is a great need for developing fast and accurate methods to analyze the security of such cryptographic modules long before a system is realized as a physical computer chip. This is due to the great resource cost in trying to address security concerns of a system already on the market, or embedded out in the field. It is hoped that the data will help in the development of a model that can assist in evaluating security concerns at a very early stage in the design process. |